OpenSSH for Windows 8.6p1
A new major update to OpenSSH for Windows (thanks to the @PowerShell team).
It comes with OpenSSH 8.6p1 and LibreSSL 3.3.3
You can download OpenSSH for Windows through the buttons below or via the binaries at the bottom of this release.
| OpenSSH for Windows x64 | OpenSSH for Windows x86 |
|---|---|
Hope you enjoy OpenSSH for Windows!
© 2020 — 2021, Lumito — www.lumito.net
OpenSSH for Windows 8.6p1-beta1
Whoah! OpenSSH for Windows 8.6p1-beta1 is now available for download. It (only) comes with OpenSSH 8.6p1 and some minor bugfixes.
NOTE: This is a beta release. That means that it may not be stable because it is under development.
You can download OpenSSH for Windows through the buttons below or via the binaries at the bottom of this release.
| OpenSSH for Windows x64 | OpenSSH for Windows x86 |
|---|---|
Hope you enjoy OpenSSH for Windows!
© 2020 — 2021, Lumito — www.lumito.net
OpenSSH for Windows 8.2p1
OpenSSH for Windows is a native port of OpenSSH to Windows. Here, in this repo, I’ve created an installer to make it easier to obtain and configure the binaries.
What’s new in version 8.2p1?
- OpenSSH version 8.2p1
- LibreSSL version 3.0.2
- Choose if you want to register SSHD and SSH-AGENT services
- Project rebranded to OpenSSH-for-Windows (before was OpenSSHforWindows-Installer)
- Other minor improvements
You can download OpenSSH for Windows through the buttons below or via the binaries at the bottom of this release.
| OpenSSH for Windows x64 | OpenSSH for Windows x86 |
|---|---|
Hope you enjoy OpenSSH for Windows!
© 2020 — 2021, Lumito — www.lumito.net
Released version 8.1
First release of OpenSSH for Windows — Installer!
It comes with this features:
- A setup wizard for x64 and x86 systems
- A modern OpenSSH version for a Windows OS
- Fully tested with various Windows 10 systems
- An old setup available by downloading the source code
You can download OpenSSH for Windows — Installer through the buttons below or via the binaries at the bottom of this release.
| OpenSSH for Windows x64 | OpenSSH for Windows x86 |
|---|---|
Hope you enjoy OpenSSH for Windows — Installer 8.1!
© 2020, Lumito — www.lumito.net
OpenSSH is a complete implementation of the SSH protocol (version 2) for secure remote login, command execution and file transfer. It includes a client ssh and server sshd, file transfer utilities scp and sftp as well as tools for key generation (ssh-keygen), run-time key storage (ssh-agent) and a number of supporting programs. This is a port of OpenBSD’s OpenSSH to most Unix-like operating systems, including Linux, OS X and Cygwin. Portable OpenSSH polyfills OpenBSD APIs that are not available elsewhere, adds sshd sandboxing for more operating systems and includes support for OS-native authentication and auditing (e.g. using PAM). There are many build-time customization options available.
Features
- Portable OpenSSH is built using autoconf and make
- It requires a working C compiler, standard library and headers
- libcrypto from either LibreSSL or OpenSSL may also be used
- OpenSSH may be built without it supporting a subset of crypto algorithms
- zlib is optional; without it transport compression is not supported
- FIDO security token support needs libfido2 and its dependencies
Project Samples
Raima Database Manager (RDM) is an embedded relational database optimized to run on resource-constrained IoT edge devices that require real-time response. RDM enables intelligent decisions to be made at the device level within microseconds.
User Ratings
5.0
out of 5 stars
★★★★★
★★★★
★★★
★★
★
ease
1 of 5
2 of 5
3 of 5
4 of 5
5 of 5
0 / 5
features
1 of 5
2 of 5
3 of 5
4 of 5
5 of 5
0 / 5
design
1 of 5
2 of 5
3 of 5
4 of 5
5 of 5
0 / 5
support
1 of 5
2 of 5
3 of 5
4 of 5
5 of 5
0 / 5
Additional Project Details
Operating Systems
Windows
- Downloads
- Internet Tools
- FTP Utilities
OpenSSH 9.3
OpenSSH is the premier connectivity tool for remote login with the SSH protocol. It encrypts all traffic to eliminate eavesdropping, connection hijacking, and other attacks.
In addition, OpenSSH provides a large suite of secure tunneling capabilities, several authentication methods, and sophisticated configuration options.
The OpenSSH suite consists of the following tools:
- Remote operations are done using ssh, scp, and sftp.
- Key management with ssh-add, ssh-keysign, ssh-keyscan, and ssh-keygen.
- The service side consists of sshd, sftp-server, and ssh-agent.
OpenSSH is developed by a few developers of the OpenBSD Project and made available under a BSD-style license.
Features
- Completely open source project with free licensing
- The OpenSSH source code is available free to everyone via the Internet. This encourages code reuse and code auditing. Code review ensures the bugs can be found and corrected by anyone. This results in secure code. OpenSSH is not covered by any restrictive license. It can be used for any and all purposes, and that explicitly includes commercial use. The license is included in the distribution. We feel that the world would be better if routers, network appliances, operating systems, and all other network devices had ssh integrated into them. All components of a restrictive nature (i.e. patents) have been removed from the source code. Any licensed or patented components are chosen from external libraries (e.g. LibreSSL).
- Strong cryptography (AES, ChaCha20, RSA, ECDSA, Ed25519…)
- Encryption is started before authentication, and no passwords or other information is transmitted in the clear. Encryption is also used to protect against spoofed packets. A number of different ciphers and key types are available, and legacy options are usually phased out in a reasonable amount of time.
- X11 forwarding (which also encrypts X Window System traffic)
- X11 forwarding allows the encryption of remote X windows traffic, so that nobody can snoop on your remote xterms or insert malicious commands. The program automatically sets DISPLAY on the server machine, and forwards any X11 connections over the secure channel. Fake Xauthority information is automatically generated and forwarded to the remote machine; the local client automatically examines incoming X11 connections and replaces the fake authorization data with the real data (never telling the remote machine the real information).
- Port forwarding (encrypted channels for legacy protocols)
- Port forwarding allows forwarding of TCP/IP connections to a remote machine over an encrypted channel. Insecure internet applications like POP can be secured with this.
- Strong authentication (public keys, one-time passwords)
- Strong authentication protects against several security problems: IP spoofing, fakes routes and DNS spoofing. Some authentication methods include public key authentication, one-time passwords with s/key and authentication using Kerberos (only in -portable).
- Agent forwarding
- An authentication agent, running in the user’s laptop or local workstation, can be used to hold the user’s authentication keys. OpenSSH automatically forwards the connection to the authentication agent over any connections, and there is no need to store the authentication keys on any machine in the network (except the user’s own local machine). The authentication protocols never reveal the keys; they can only be used to verify that the user’s agent has a certain key. Eventually the agent could rely on a smart card to perform all authentication computations.
- Interoperability
- Interoperability between implementations is a goal, but not a promise. As OpenSSH development progresses, older protocols, ciphers, key types and other options that have known weaknesses are routinely disabled. Some examples can be found on the legacy page.
- SFTP client and server support.
- Complete SFTP support is included, using the sftp(1) command as a client and sftp-server(8) subsystem as a server.
- Optional data compression
- Data compression before encryption improves the performance for slow network links.
What’s New
OpenSSH 9.1 was released on 2022-10-04. OpenSSH is a 100% complete SSH protocol 2.0 implementation and includes sftp client and server support.
- It is now possible[1] to perform chosen-prefix attacks against the
- SHA-1 algorithm for less than USD$50K.
- In the SSH protocol, the «ssh-rsa» signature scheme uses the SHA-1 hash algorithm in conjunction with the RSA public key algorithm. OpenSSH will disable this signature scheme by default in the near future.
- Note that the deactivation of «ssh-rsa» signatures does not necessarily require cessation of use for RSA keys. In the SSH protocol, keys may be capable of signing using multiple algorithms. In particular, «ssh-rsa» keys are capable of signing using «rsa-sha2-256» (RSA/SHA256), «rsa-sha2-512» (RSA/SHA512) and «ssh-rsa» (RSA/SHA1). Only the last of these is being turned off by default.
- This algorithm is unfortunately still used widely despite the existence of better alternatives, being the only remaining public key signature algorithm specified by the original SSH RFCs that is still enabled by default.
Security
- This release contains fixes for three minor memory safety problems. None are believed to be exploitable, but we report most memory safety problems as potential security vulnerabilities out of caution.
- ssh-keyscan(1): fix a one-byte overflow in SSH- banner processing. Reported by Qualys
Potentially-incompatible changes
This release includes a number of changes that may affect existing configurations:
- ssh(1), sshd(8): this release changes the first-preference signature algorithm from ECDSA to ED25519.
- ssh(1), sshd(8): set the TOS/DSCP specified in the configuration for interactive use prior to TCP connect. The connection phase of the SSH session is time-sensitive and often explicitly interactive. The ultimate interactive/bulk TOS/DSCP will be set after authentication completes.
- ssh(1), sshd(8): remove the pre-standardization cipher rijndael-cbc@lysator.liu.se. It is an alias for aes256-cbc before it was standardized in RFC4253 (2006), has been deprecated and disabled by default since OpenSSH 7.2 (2016) and was only briefly documented in ssh.1 in 2001.
- ssh(1), sshd(8): update/replace the experimental post-quantum hybrid key exchange method based on Streamlined NTRU Prime coupled with X25519.
- The previous sntrup4591761x25519-sha512@tinyssh.org method is replaced with sntrup761x25519-sha512@openssh.com. Per its designers, the sntrup4591761 algorithm was superseded almost two years ago by sntrup761. (note this both the updated method and the one that it replaced are disabled by default)
- ssh(1): disable CheckHostIP by default. It provides insignificant benefits while making key rotation significantly more difficult, especially for hosts behind IP-based load-balancers.
Changes
New features
- ssh(1): this release enables UpdateHostkeys by default subject to some conservative preconditions:
- The key was matched in the UserKnownHostsFile (and not in the GlobalKnownHostsFile).
- The same key does not exist under another name.
- A certificate host key is not in use.
- known_hosts contains no matching wildcard hostname pattern.
- VerifyHostKeyDNS is not enabled.
- The default UserKnownHostsFile is in use.
- We expect some of these conditions will be modified or relaxed in future.
- ssh(1), sshd(8): add a new LogVerbose configuration directive for that allows forcing maximum debug logging by file/function/line pattern-lists.
- ssh(1): when prompting the user to accept a new hostkey, display any other host names/addresses already associated with the key.
- ssh(1): allow UserKnownHostsFile=none to indicate that no known_hosts file should be used to identify host keys.
- ssh(1): add a ssh_config KnownHostsCommand option that allows the client to obtain known_hosts data from a command in addition to the usual files.
- ssh(1): add a ssh_config PermitRemoteOpen option that allows the client to restrict the destination when RemoteForward is used with SOCKS.
- ssh(1): for FIDO keys, if a signature operation fails with a «incorrect PIN» reason and no PIN was initially requested from the user, then request a PIN and retry the operation. This supports some biometric devices that fall back to requiring PIN when reading of the biometric failed, and devices that require PINs for all hosted credentials.
- sshd(8): implement client address-based rate-limiting via new sshd_config(5) PerSourceMaxStartups and PerSourceNetBlockSize directives that provide more fine-grained control on a per-origin address basis than the global MaxStartups limit.
Bugfixes
- ssh(1): Prefix keyboard interactive prompts with «(user@host)» to make it easier to determine which connection they are associated with in cases like scp -3, ProxyJump, etc. bz#3224
- sshd(8): fix sshd_config SetEnv directives located inside Match blocks. GHPR201
- ssh(1): when requesting a FIDO token touch on stderr, inform the user once the touch has been recorded.
- ssh(1): prevent integer overflow when ridiculously large ConnectTimeout values are specified, capping the effective value (for most platforms) at 24 days. bz#3229
- ssh(1): consider the ECDSA key subtype when ordering host key algorithms in the client.
- ssh(1), sshd(8): rename the PubkeyAcceptedKeyTypes keyword to PubkeyAcceptedAlgorithms. The previous name incorrectly suggested that it control allowed key algorithms, when this option actually specifies the signature algorithms that are accepted. The previous name remains available as an alias. bz#3253
- ssh(1), sshd(8): similarly, rename HostbasedKeyTypes (ssh) and HostbasedAcceptedKeyTypes (sshd) to HostbasedAcceptedAlgorithms.
- sftp-server(8): add missing lsetstat@openssh.com documentation and advertisement in the server’s SSH2_FXP_VERSION hello packet.
- ssh(1), sshd(8): more strictly enforce KEX state-machine by banning packet types once they are received. Fixes memleak caused by duplicate SSH2_MSG_KEX_DH_GEX_REQUEST (oss-fuzz #30078).
- sftp(1): allow the full range of UIDs/GIDs for chown/chgrp on 32bit platforms instead of being limited by LONG_MAX. bz#3206
- Minor man page fixes (capitalization, commas, etc.) bz#3223
- sftp(1): when doing an sftp recursive upload or download of a read-only directory, ensure that the directory is created with write and execute permissions in the interim so that the transfer can actually complete, then set the directory permission as the final step. bz#3222
- ssh-keygen(1): document the -Z, check the validity of its argument earlier and provide a better error message if it’s not correct. bz#2879
- ssh(1): ignore comments at the end of config lines in ssh_config, similar to what we already do for sshd_config. bz#2320
- sshd_config(5): mention that DisableForwarding is valid in a sshd_config Match block. bz3239
- sftp(1): fix incorrect sorting of «ls -ltr» under some circumstances. bz3248.
- ssh(1), sshd(8): fix potential integer truncation of (unlikely) timeout values. bz#3250
- ssh(1): make hostbased authentication send the signature algorithm in its SSH2_MSG_USERAUTH_REQUEST packets instead of the key type.
- This make HostbasedAcceptedAlgorithms do what it is supposed to — filter on signature algorithm and not key type.
Portability
- sshd(8): add a number of platform-specific syscalls to the Linux seccomp-bpf sandbox. bz#3232 bz#3260
- sshd(8): remove debug message from sigchld handler that could cause deadlock on some platforms. bz#3259
- Sync contrib/ssh-copy-id with upstream.
- unittests: add a hostname function for systems that don’t have it. Some systems don’t have a hostname command (it’s not required by POSIX). The do have uname -n (which is), but not all of those have it report the FQDN.
Fast servers and clean downloads. Tested on TechSpot Labs. Here’s why you can trust us.
Last updated:
User rating:
11 votes
Software similar to OpenSSH 4
-
62 votes
PuTTY is a free implementation of Telnet and SSH.
- Freeware
- Windows/Linux
-
23 votes
KiTTY is a fork from version of PuTTY, the best telnet / SSH client in the world. KiTTY is only designed for the Microsoft Windows platform.
- Freeware
- Windows
-
183 votes
SecureCRT is a Windows terminal emulator that supports Secure Shell (SSH), Telnet, rlogin, serial, and TAPI protocols.
- Free to Try
- Windows/macOS/Linux
-
More similar downloads
Popular apps
in FTP Utilities

Join the Chocolatey Team on our regular monthly stream where we discuss all things Community, what we do, how you can get involved and answer your Chocolatey questions.

Join the Chocolatey Team on our regular monthly stream where we put a spotlight on the most recent Chocolatey product releases. You’ll have a chance to have your questions answered in a live Ask Me Anything format.

Livestream from
Thursday, 06 October 2022
We recently released our largest update to Chocolatey Central Management so far. Join Gary and Steph to find out more about Chocolatey Central Management and the new features and fixes we’ve added to this release.
Watch On-Demand

Webinar Replay from
Wednesday, 30 March 2022
At Chocolatey Software we strive for simple, and teaching others. Let us teach you just how simple it could be to keep your 3rd party applications updated across your devices, all with Intune!
Watch On-Demand

Livestream from
Thursday, 9 June 2022
Join James and Josh to show you how you can get the Chocolatey For Business recommended infrastructure and workflow, created, in Azure, in around 20 minutes.
Watch On-Demand

Livestream from
Thursday, 04 August 2022
Join Paul and Gary to hear more about the plans for the Chocolatey CLI in the not so distant future. We’ll talk about some cool new features, long term asks from Customers and Community and how you can get involved!
Watch On-Demand

Livestreams from
October 2022
For Hacktoberfest, Chocolatey ran a livestream every Tuesday! Re-watch Cory, James, Gary, and Rain as they share knowledge on how to contribute to open-source projects such as Chocolatey CLI.
Watch On-Demand

Livestream from
Thursday, 03 November 2022
Join Paul and Gary for this months Chocolatey product livestream where we look at the latest release of Chocolatey 1.2.0, Chocolatey Licensed Extension 5.0.0 and shine a spotlight on the new hook scripts functionality. This opens up so many possibilities for Chocolatey CLI users!
Watch On-Demand

Livestream from
Tuesday, 29 November 2022
Join Josh as he adds the ability to manage Chocolatey GUI config and features with the Chocolatey Ansible Collection.
Watch On-Demand
Webinar from
Tuesday, 13 December 2022
Join Gary, Paul, and Maurice as they introduce and demonstrate how to use Chocolatey! Questions will be answered live in an Ask Me Anything format.
Watch On-Demand
One of the biggest and most welcome changes to the Windows 10 1809 update and in Windows Server 2019 was the addition of the OpenSSH Client and OpenSSH Server features. It is now incredibly easy to SSH into a Windows Workstation/Server using native tools that are now builtin to the Operating System. In the past this was only possible by using complicated tools and odd workarounds in order to get an SSH-like implementation to work correctly. You can also use the SSH commands right from the Windows command line (CMD, PowerShell), without needing third-party tools or odd commands. This is a very nice change that Microsoft has added, since it is much easier to remotely manage a Windows through the Command Line instead of the GUI, and having the ability to use the same tools on both Windows and Linux is a big advantage.
Note: I have only tested this on Windows 10 Pro for Workstations (Version 1809 Build 17763.253) and on Windows Server 2019 Standard.
Table Of Contents
Installation
Installing the OpenSSH Client and OpenSSH Server options can be done through either the Settings app or through the Command Line.
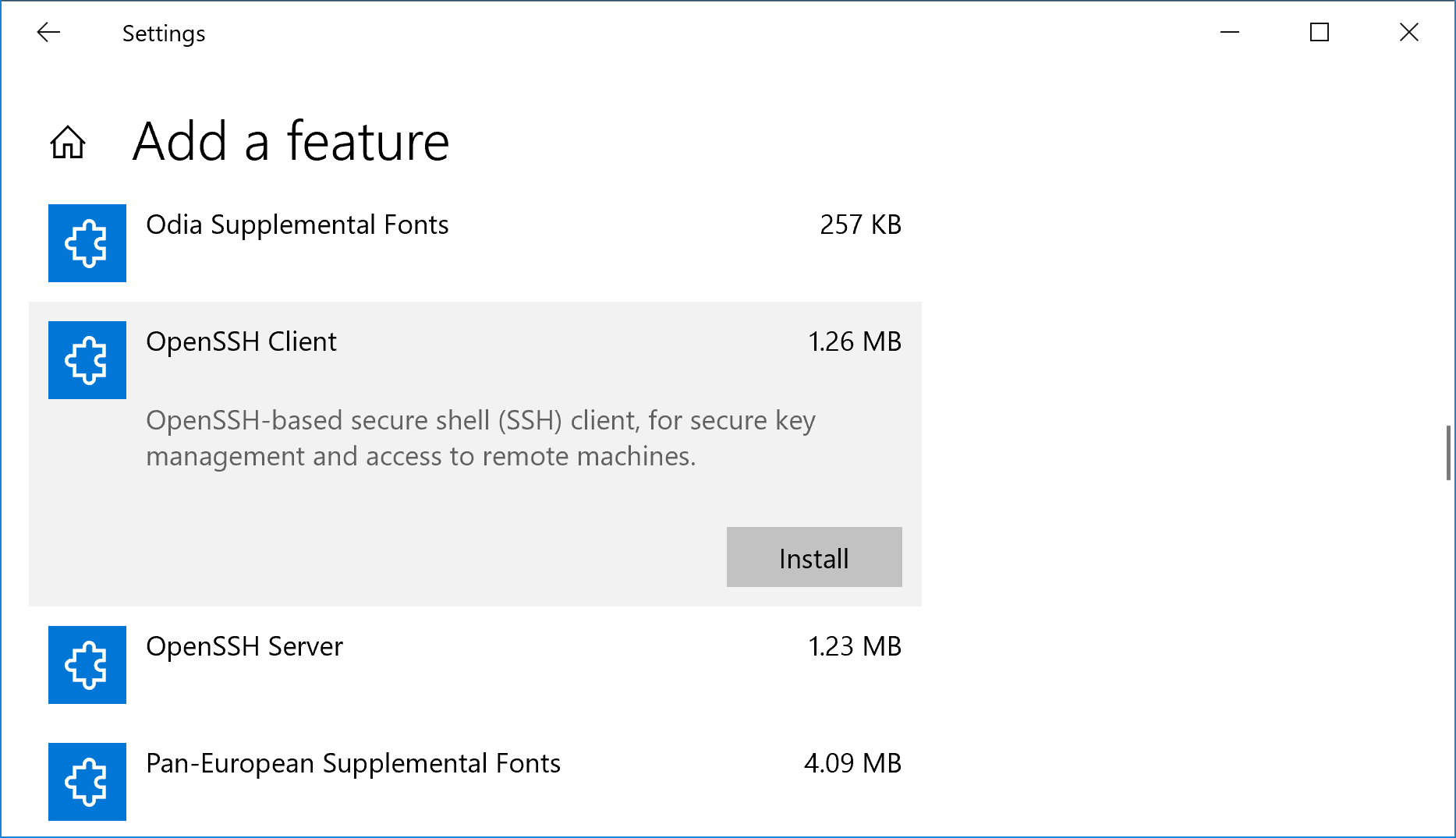
GUI Installation
To install through the GUI, go to Settings -> Apps -> Apps & Features -> Manage optional features -> Add a feature. You should see the two options in the list of available features that can be installed:
- OpenSSH Client
- OpenSSH Server
Highlight each option and click the Install button to install the feature. If the options are missing, then you are not on the latest version/patch level of Windows 10 or Windows Server 2019. A restart should not be necessary after adding these features, but the newly installed services will need to be started and configured to automatically start at boot.
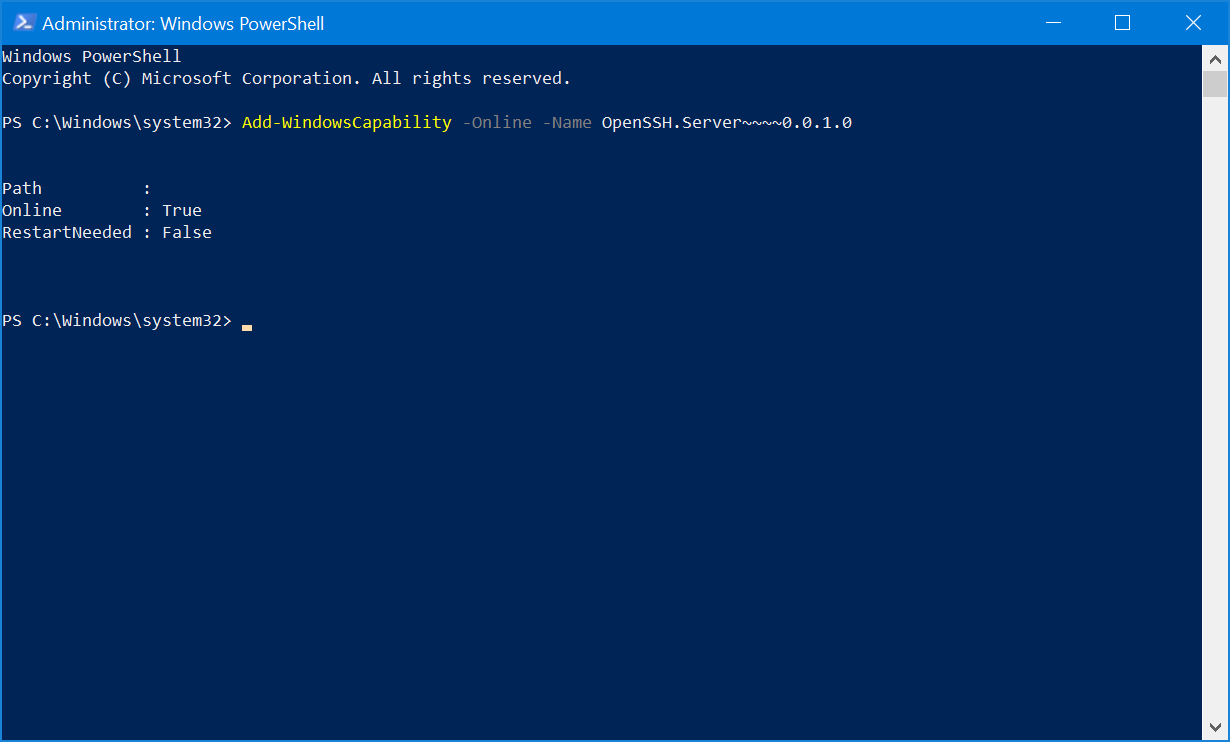
Command Line Installation
To install through the Command Line, open an elevated PowerShell console in order to proceed. To confirm that you are able to install the OpenSSH Client and OpenSSH Server features, run the following command:
Get-WindowsCapability -Online | findstr OpenSSH
Name : OpenSSH.Client~~0.0.1.0
Name : OpenSSH.Server~~0.0.1.0
If those two options are present, run the following two commands to install the features:
Add-WindowsCapability -Online -Name OpenSSH.Client~~~~0.0.1.0
Add-WindowsCapability -Online -Name OpenSSH.Server~~~~0.0.1.0
Like installing through the Settings app, a restart should not be necessary after adding these features. The newly installed services will need to be started and configured to automatically start at boot.
Services Start
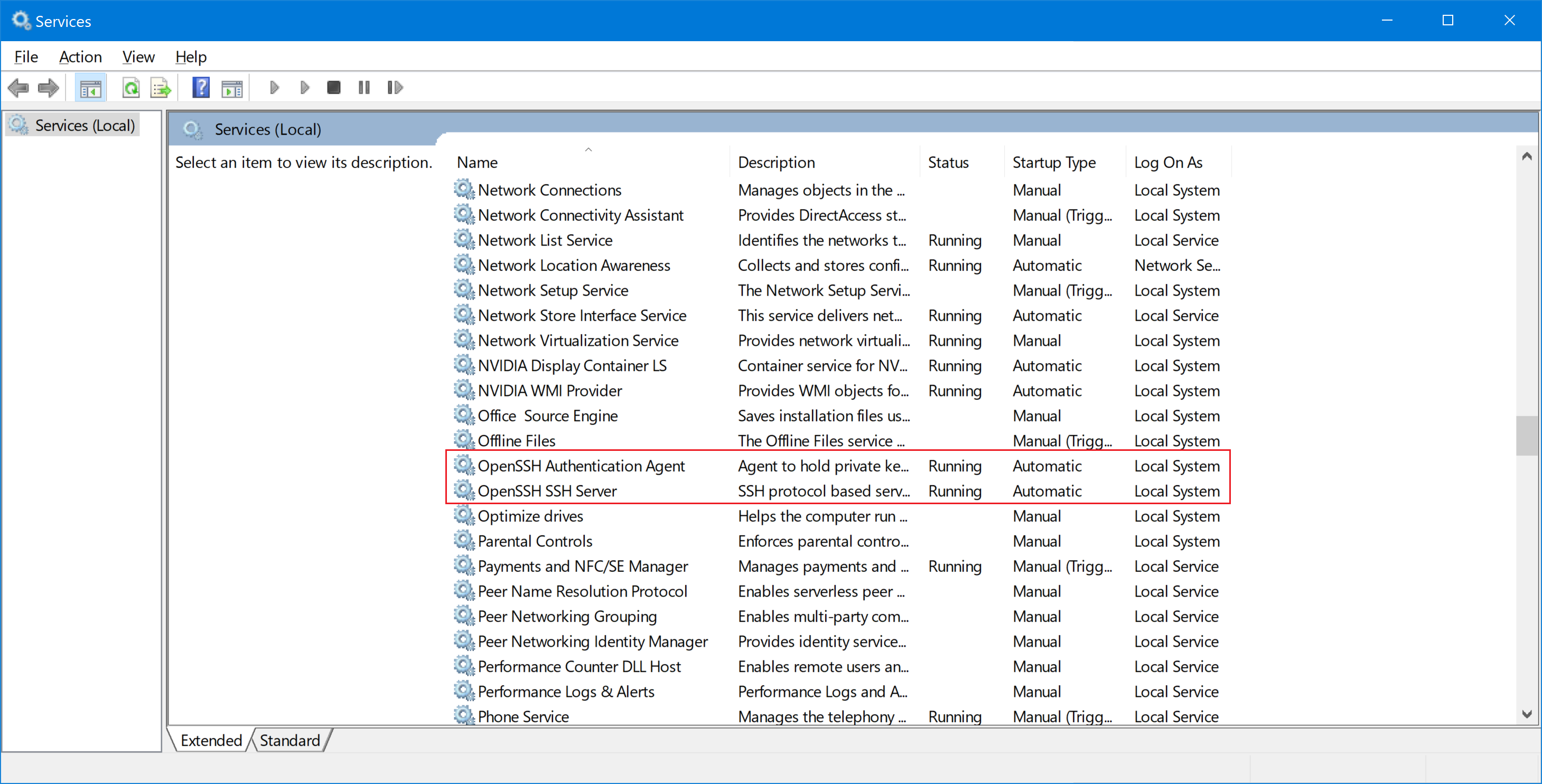
In order to start using OpenSSH Server, the associated services will need to be started first. This can be done through either the Services MMC console or through the Command Line.
Services MMC Console
Open the Services MMC Console (Win + R, and type in services.mmc) and find the two Services that are related to OpenSSH Server:
- OpenSSH Authentication Agent
- OpenSSH Server
Right-click on each service and select Properties. Under Service Status, click the Start button to start the service. To configure the service to start automatically at boot, change the Startup Type drop-down menu to Automatic and click Apply.
Command Line Services
To start the OpenSSH Server services and enable them to run automatically, there are a few command that you will need to run. To do this, open an elevated PowerShell console and run the following commands to start the OpenSSH Server:
Start-Service sshd
Start-Service ssh-agent
To have these services start automatically at boot, there are two additional commands to run as well:
Set-Service sshd -StartupType Automatic
Set-Service ssh-agent -StartupType Automatic
After this has been completed, you should be able to connect to your Windows installation over SSH.
Using OpenSSH Client
The OpenSSH Client can be used exactly the same way as you would on any Linux/Unix host. It will work through the regular Command Line and in PowerShell:
PS C:\> ssh.exe
usage: ssh [-46AaCfGgKkMNnqsTtVvXxYy] [-B bind_interface]
[-b bind_address] [-c cipher_spec] [-D [bind_address:]port]
[-E log_file] [-e escape_char] [-F configfile] [-I pkcs11]
[-i identity_file] [-J [user@]host[:port]] [-L address]
[-l login_name] [-m mac_spec] [-O ctl_cmd] [-o option] [-p port]
[-Q query_option] [-R address] [-S ctl_path] [-W host:port]
[-w local_tun[:remote_tun]] destination [command]
Here is the same output from a Linux environment:
matthew@thinkpad / $ ssh
usage: ssh [-46AaCfGgKkMNnqsTtVvXxYy] [-b bind_address] [-c cipher_spec]
[-D [bind_address:]port] [-E log_file] [-e escape_char]
[-F configfile] [-I pkcs11] [-i identity_file]
[-J [user@]host[:port]] [-L address] [-l login_name] [-m mac_spec]
[-O ctl_cmd] [-o option] [-p port] [-Q query_option] [-R address]
[-S ctl_path] [-W host:port] [-w local_tun[:remote_tun]]
[user@]hostname [command]
I won’t go into the details on how to use any of these advanced options, there are very good tutorials on how to use the OpenSSH Client on other sites. The behaviour of OpenSSH Client on Windows should be almost exactly the same as on a Linux environment. So far I haven’t run into any issues with connectivity.
Connecting to OpenSSH Server
There is nothing special required to connect to a Windows host, it behaves exactly the same way as any other SSH host. There are a few different username formats that you can use:
user@windows-host (Local User Account)
user@domain.local@windows-host (Domain UPN)
domain\user@windows-host (Netbios)
One of the benefits is the ability to login with a Microsoft account if you are using that as your username. It is a bit unusual to see an e-mail address used this way, but I am glad that Microsoft made sure that this functionality worked correctly:
user@outlook.com@windows-host
There is nothing more to OpenSSH Server, you can manage your Windows host from the command line once you are logged in. If you want to do any further customization or need some basic troubleshooting, there is additional information below.
Change the Default Shell
By default when you login to a Windows installation with SSH, it defaults to the regular Command Prompt (cmd.exe). I prefer PowerShell for everyday usage, and it is easy to switch to PowerShell once you login, but you can change the default shell to save yourself some time if you are going to be using this feature often.
This is done through the Registry Editor, which will run with Administrator privileges. You need to navigate to the following key:
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\OpenSSH
Create a new string called DefaultShell and give it the following value:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe
Restart the OpenSSH Server Service and the next time that you login with SSH, you should automatically go to PowerShell. I have tried making this work with Bash, but it doesn’t seem to be supported yet.
If you do want to use Bash, just type in bash.exe to switch to it.
Additional Settings
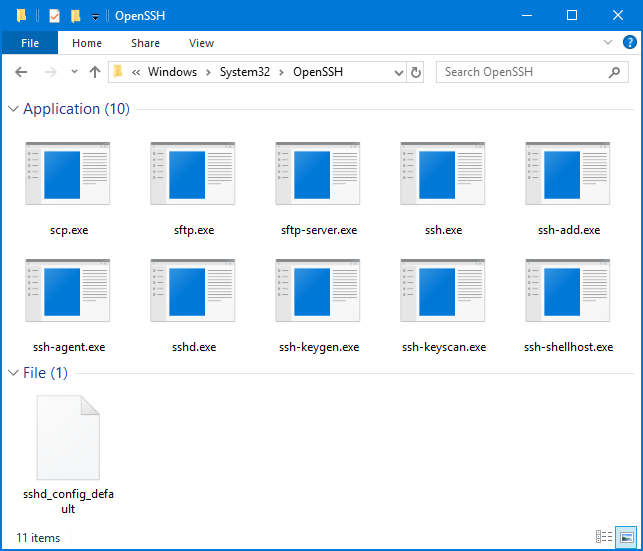
There are a few customizations that you can do to the OpenSSH Server service if needed. Since this is a port of the OpenSSH Server, the customization is done in a very similar way. To begin, the directory where all of the associated executable files are found is in the C:\Windows\System32\OpenSSH directory:
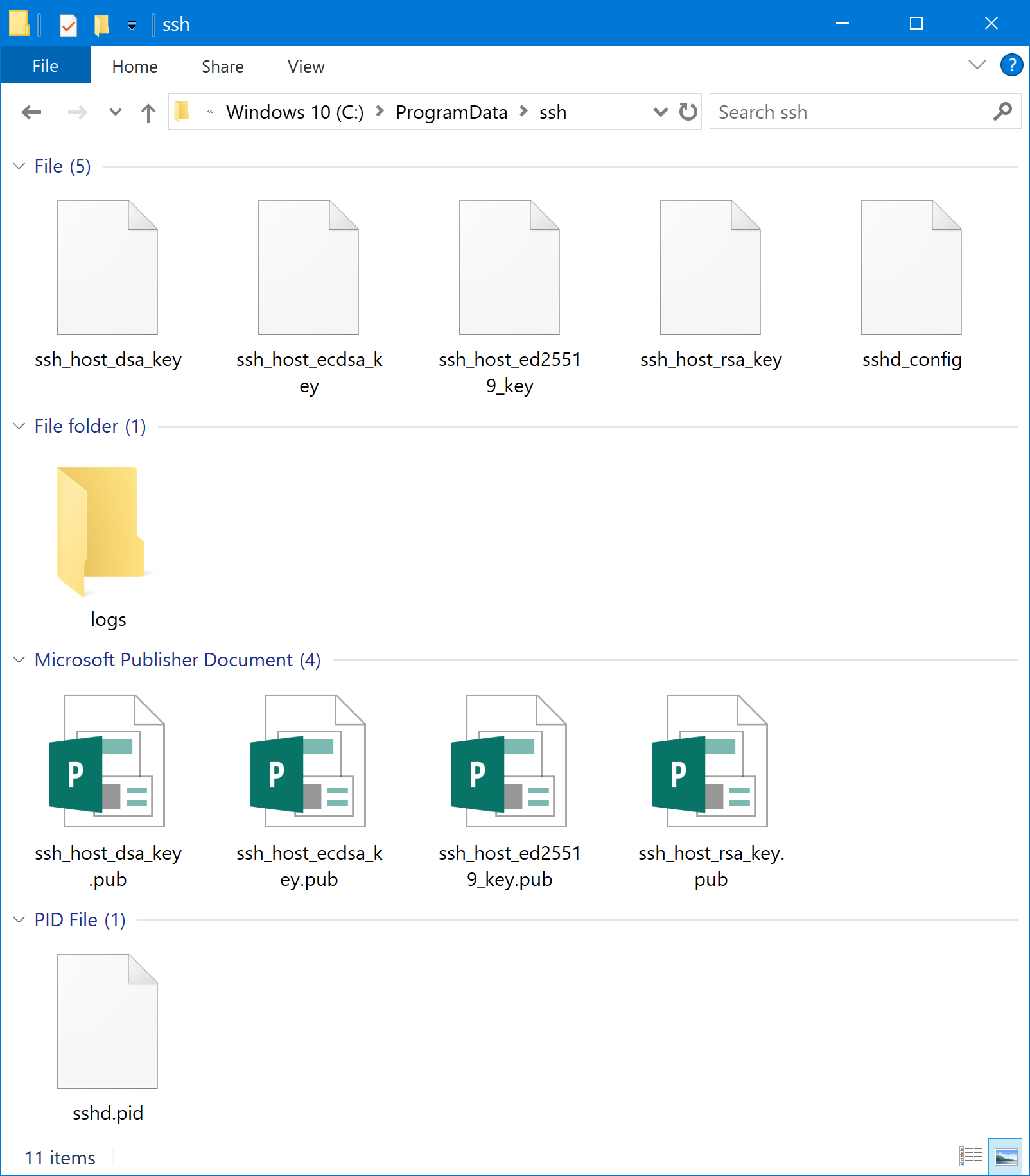
The other important directory for OpenSSH Server is the C:\ProgramData\ssh folder, which contains the configuration files and log files.
OpenSSH Server options, such as changing the login banner and locking down security options are done in the C:\ProgramData\ssh\sshd_config file.
Not all options can be used on a Windows host. For more information, you can refer to the official Wiki article on what options are supported:
https://github.com/PowerShell/Win32-OpenSSH/wiki/sshd_config
Troubleshooting
If you need to view the log file for OpenSSH Server, you need to make a quick change to the configuration file (C:\ProgramData\ssh\sshd_config) to enable logging:
# Logging
#SyslogFacility AUTH
#LogLevel INFO
Make the following change:
# Logging
SyslogFacility LOCAL0
LogLevel INFO
You will need to restart the OpenSSH Server service in order to apply the change. Once the change has been made, the log file (sshd.log) can be found in the C:\ProgramData\ssh\logs directory. When you are finished troubleshooting, you should revert this change to prevent unnecessary logging for the OpenSSH service.
Links
- SSH on Windows Server 2019
- Win32-OpenSSH